Electronic warfare is a new generation of warfare that is supported by the latest technologies. With the technology we used so far most of the things around us working with the electronic cards. Even the electrical systems are controlled with electronic systems. So if you have control over an electronic system, you have the control over the electrical system or device.
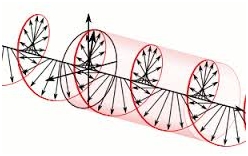
The advanced technology let us use electromagnetic waves in a way that we can jam signals, destruct or suppress an electronic system. Using electromagnetic waves in this way lets us use this technology as a kind of gun. You must have seen these kinds of things in movies but these are the things used in real life as well and lots of engineers and scientists are working on this kind of systems.
Actually electronic war consists of electronic defense, electronic attack and support systems.
1.The Nature of Electromagnetic Waves and Its effects on Electronic Systems
Simply from high school physics you must remember the electromagnetic waves or from a university course. The most basic model of electromagnetic waves in fact is defined by Faraday.
When there were just forces that we can see the effects of it (mechanical forces), some of the scientists found that a compass that is put just near to a cable, that electricity flows through it, deflected by an invisible “thing”. That “thing” was the electromagnetic force.
Faraday unlike the scientists in his time could define this relation between electricity and magnetism and could visualize them. So in a very basic way electricity passing through a piece of wire applies some force that is near to it. If we look at the situation in a reversed angle electromagnetic force applied on a wire would do the opposite thing and will create a virtual current.
This is where the electromagnetic attack idea comes from.
If we apply electromagnetic field to a living circuit (circuit that works properly), we may make it work different, we may suppress the waves going through or out of the circuit (cut the communication) or even more we may destruct the circuit fully so that it will be out of service (burning the circuit or components of the target circuit or system).
Thinking by this way you can understand why we need to close our mobile phones in the bus or an airplane (Although there are experiments prove that we don’t need to). One mobile may not be effective to take down an airplane but if hundreds of mobile devices are on this may take down an airplane (although it has tiny power compared to real electromagnetic attacks).
Not to cause these types of results latest electronic equipments are tested against electromagnetic fields and EMC (electromagnetic compatibility). Here the important point is the EMC laws and regulations. Every device must be compatible with these regulations.
2.Types of Electromagnetic Attacks
Jamming
Jamming may be used for radio signals, mobile phone signals or radar signals. In a war the aims is simply cutting the communication through the air of the opponent and make them lose control of the war. Here the tricky point is adjusting your frequency with the opponent’s frequency so that you can give enough power to the jammer that suppresses that frequency.
There are lots of different sub-branch and techniques for jamming like Bluetooth jamming, radar jamming etc. Every attack needs its own special method of attack.
To survive from these kinds of attacks you need to change frequency continuously according to a hidden algorithm that is known by the two sides of the communication or remove the jammer in a physical way or simply decide to change frequency to another.
Deciding frequency change through a radio communication is not a safe way in a war since probably the line will be listened by the opponent so a hidden algorithm for frequency change is better.
2.2 Electromagnetic Destruction of Electronic Equipments (Destructive Attacks)
You may prefer directly destructing the target electronic equipment by using electromagnetic waves. In this way you will use more than enough power since the aim here is to destruct the equipment fully. You may think that it is not possible to destruct electronic equipment but think about the coils that we used to melt metals in the industry. We may even burn circuits.
This is not only to use by military also bank robberies are possible by jamming and destructing so that the communication systems of a bank will be off (If there is no wired emergency system). The defense against this kind of attack is only possible by a fully working electromagnetic defense system that can define the direction of the flux and can react back as soon as possible since the waves used are destructive.
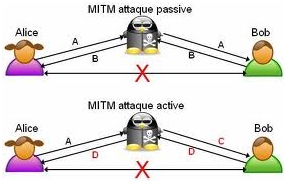
2.3 Man in the Middle (Network attacks, hacking, spying)
Men in the middle attack is a type of cryptographic attack done by listening to the endpoints of a network line and try to get some information. These kinds of attacks are called hack and used by spies also.
You may easily get information by using one of these kinds of attacks by mimicking the elements of a radio network and sitting in the middle sniffing the signals. These are all about signal processing and in informative magnetic waves the things you can do are endless. Waves are always there and open to attack.
The defense solution against these kinds of attacks is to have a secure network configuration and keeping eye on the latest cryptographic technologies and updating security systems since everyday a new type of open gate is found by the hackers.
Another solution to this problem may be using jammer. Yes although it is listed as an attack system if you use it against network spying it will be a type of defense system and jammers are widely used where hidden meetings need to be done and if you don’t want spies’ ears in the room.
2.4 Biological Threads
The waves are not good for human body and may lead to death if you have an electronic equipment like heart battery integrated into body. Although it is not very powerful every device that works with electricity has some magnetic field around it. The level magnetic field they propagate must be kept under some level, all defined by standarts.
3. Electromagnetic Defense Systems
An electromagnetic defense system simply must consist of antennas, a signal processing unit and response systems. The idea is simple; you gather the signals around by using antennas (you need different antennas for different signal types) and you process them by using a processor, by this way you can get the direction, power and type of an attack.
As a result, according to the program written in the processor unit the system responses back for protection or counter attack if possible. These kind of systems are not very developed and need further researches.
Conclusion
Technology comes with responsibilities. Every new technology comes with bad and good sides like atom bomb, electromagnetic waves and medicines. The only thing we can do is to find effective protection methods against attacks.
The best method against EM attacks is using a fully capable electromagnetic defense system. If you don’t need that complex system you may use jammer as a wave suppressor or in a war you may use cryptographic frequency system.



Hello,
Is there a way to help me. I have been victimized for more than four years by direct electromagnetic attacks. There is no rest for me. No matter where I am – even in Europe – the horrible attacks continue relentlessly. Besides the waves penetrating any place I lay down, on the floor, in the bathtub, in a closet, there are these flying little particles which go everywhere in my body – even inside my ears, eyes, nose, mouth; my mouth tastes bitter, dry, painful. I think these particles go from my ears to my mouth. I keep my ears covered now, but the particles are so aggressive that they are able to penetrate my ears. The bottom of my feet and the legs are totally electrified. When I walk my angles become so heavy, but if I use a wet cloth or scratch on them, for a short time I don’t feel anything. I use a fan constantly – night and days – since it helps to keep, not totally, the particles away. When I take a shower, I hardly feel them. Also, the strong wind outside slows them down.
What can I do to help myself with this horrible suffering? Can you give me some advises? I delt with the medical system; I went through all kinds of tests and took different medication; I new nothing would solve my problem and was hopping the doctors would agree with me. What a terrible mistake I made! They see it only their way. They released three reports each one with a different diagnosis. At the end they decided that my problem was mental.
Any notification. Will be greatly appreciated.
Anna Biondi
you are a Targetted Individual amoug many millions in the world I have been A TI 32 years in the UK It is truely appaulling what they are doing to us I hope you are still trying to sheild Best wishes Liz